Unlicensed transfers: EU technical data risks with unvetted translators
- 13 minutes ago
- 7 min read
Handing a classified technical manual to a translation vendor feels routine. It is not. Under EU Regulation 2021/821, transmitting controlled defense technical data to an unvetted linguist, regardless of where that linguist sits, can constitute an unlicensed transfer of technology. The consequences range from NCA enforcement action to criminal liability for the responsible compliance officer. This article explains exactly how the regulation defines technology transfer, why translation workflows trigger export controls, what authorisation obligations apply, and how EU defense primes can build a vetting framework that satisfies both the letter and the spirit of the law.
Table of Contents
Key Takeaways
Point | Details |
Translation triggers export risk | Sharing defense technical data with unvetted translators is treated as an export under EU law. |
Authorisation is often required | You typically need prior approval before transferring sensitive defense data for translation. |
Vetting translators prevents violations | Properly vetting translators and controlling access helps avoid unlicensed transfers and legal penalties. |
Annex IV and national lists matter | Special rules may apply even for intra-EU transfers based on regulatory item classifications. |
What does EU Regulation 2021/821 cover?
Most compliance teams think of export controls as applying to physical goods crossing a border. The regulation is far broader than that. Dual-use items include technology, which explicitly covers controlled defense technical data in any format, whether printed, digital, or transmitted verbally. That single definitional choice changes everything for translation workflows.
The regulation also defines technical assistance in terms that capture translation directly. Article 2(9) defines technical assistance as any transmission of working knowledge or technology by any means, including electronic transmission, fax, telephone, or making it available to a third party. A linguist receiving a controlled document is, by that definition, receiving a technology transfer.
Key items covered under the regulation that defense primes routinely translate include:
Technical specifications and engineering drawings for controlled platforms
Software documentation for weapons guidance or electronic warfare systems
Maintenance and repair manuals for Annex I listed equipment
Test and evaluation reports containing performance parameters
Training materials that convey operational know-how
“The scope of ‘technology’ under EU Regulation 2021/821 is intentionally wide. If the information would give a recipient meaningful insight into the design, production, or use of a controlled item, it is controlled technology regardless of the medium.”
Understanding the deemed export risk embedded in translation is the first step. The second is recognizing that translation data security is not a vendor IT problem. It is a compliance obligation that sits with the exporting organization.
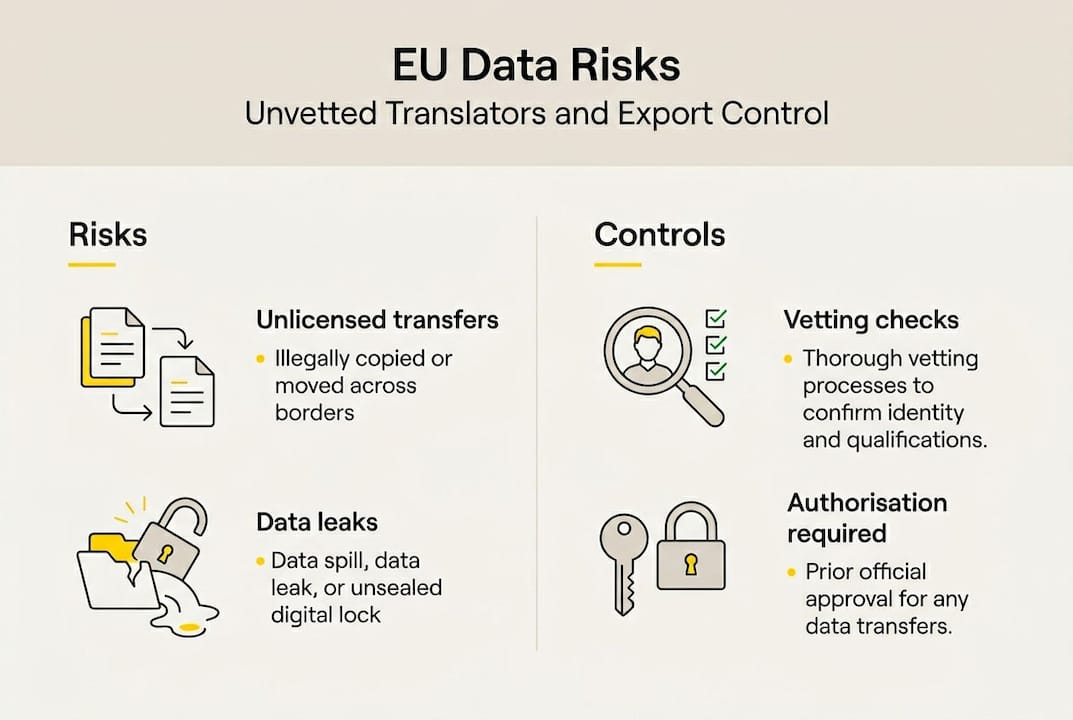
Why translation triggers export controls
With the regulation’s scope clear, here is why translation can actually trigger export controls under EU law. The mechanism is what practitioners call a deemed transfer. You do not need to send data across a border. You need only make controlled technology available to a person who is not authorized to receive it.
The technology transfer controls framework treats making technology available to a translator as equivalent to technical assistance or transfer, requiring vetting and potential authorisation. The nationality of the linguist matters because a non-EU national accessing controlled data may trigger a deemed export to their country of nationality, even if they are physically present in an EU member state.
Here is the sequence of risk that compliance officers need to map:
Identify the classification status of the document before it leaves your secure environment.
Determine the nationality and security clearance of every linguist who will access the content.
Assess whether the receiving LSP operates on public cloud infrastructure, which creates additional unauthorized access exposure.
Confirm contractual controls including NDAs, data handling obligations, and audit rights are in place before transmission.
Log the transfer with sufficient detail to satisfy NCA audit requirements from bodies such as Bafa (Germany), DGA (France), or UAMA (Italy).
Pro Tip: Treat every linguist as an end-user in your export compliance system. Run the same due diligence you would apply to a foreign customer receiving controlled hardware.
The comparison below shows how different translation approaches perform against the key compliance risk factors:
Risk factor | Legacy MT engines | Public NMT / SaaS tools | Vetted LSP with ISO 27001 |
Data sovereignty | None | Variable, often US cloud | EU-hosted, contractually defined |
Linguist vetting | No human access | Minimal or none | Full background and nationality checks |
Terminology governance | Weak | Inconsistent | Enforced via TM and TB |
Audit trail | None | Limited | Full access logs and QA records |
NCA enforcement exposure | High | High | Low when controls are verified |
The defense localization security posture of your LSP is not a procurement checkbox. It is a compliance control. Similarly, cloud risks for defense translation are a live enforcement concern, and machine translation risks in regulated contexts go well beyond terminology errors.
Critical authorisation requirements and edge cases
Understanding transfer risk is just the start. Let us look at the compliance authorisation requirements and address special cases that catch even experienced teams off guard.
Article 8 requires authorisation for the provision of technical assistance related to Annex I dual-use items where the provider is aware of prohibited end-uses. Sending a controlled document to a translator who lacks the appropriate clearance or vetting satisfies the awareness threshold if your compliance team has not performed due diligence.
Edge cases that regularly create enforcement exposure:
Scenario | Control trigger | Authorisation likely needed? |
Intra-EU transfer to vetted linguist | Annex IV items or national military lists | Yes, for sensitive Annex IV items |
EU-based linguist with non-EU nationality | Deemed export to country of nationality | Yes, depending on destination country |
Translation via public cloud platform | Unauthorized third-party access | Yes, organizational controls required |
Subcontracting to second-tier LSP | Chain of custody break | Yes, prime retains liability |
Intra-EU transfers of sensitive Annex IV items require authorisation, and defense technical data frequently falls under dual-use or national military controls that member states apply independently. France’s DGA and Germany’s Bafa both maintain national lists that extend beyond the EU common list.
The translator must be treated as an end-user requiring full due diligence. That means:
Verifying nationality and confirming no restricted country connections
Checking for existing security clearances where the data classification demands it
Requiring signed end-user undertakings, not just standard NDAs
Restricting access to the minimum data set needed for the translation task
Retaining records for the NCA audit window, which is typically five years
“The prime contractor does not transfer liability by outsourcing translation. If the LSP is unvetted, the prime is the exporter of record and bears full enforcement exposure.”
For a structured approach to evaluating high-risk vendors, a dedicated translation security checklist is a practical starting point. Building a secure technical translation process from the ground up is more efficient than retrofitting controls after an NCA inquiry.
Best practices: Vetting translators and controlling data access
With the legal requirements clear, here is how compliance teams can put that knowledge into action. The organizational measures needed to prevent unauthorized access by unvetted persons are not optional guidance. They are the compliance baseline NCAs expect to see documented.
A practical vetting framework for translation suppliers covers four areas:
Corporate due diligence. Confirm the LSP’s legal jurisdiction, ownership structure, and whether any parent entities are located in restricted countries. Request evidence of ISO 27001 certification and ask specifically whether the certification covers the infrastructure used for your data.
Linguist-level screening. Require the LSP to disclose the nationality of every linguist assigned to your project. For Annex I or national list items, require security clearance documentation. This is non-negotiable for defense primes.
Infrastructure controls. Confirm that translation processing occurs on EU-hosted, private infrastructure. Public cloud platforms, including widely used SaaS translation tools, create unauthorized third-party access exposure that is difficult to document for NCA purposes.
Contractual architecture. Go beyond a standard NDA. Your supplier agreement should specify data handling obligations, subcontracting restrictions, audit rights, breach notification timelines, and the right to inspect access logs on demand.
Pro Tip: Ask your LSP for a sample audit log from a previous defense project. If they cannot produce one, that tells you everything you need to know about their compliance posture before you sign anything.
Common pitfalls that create enforcement exposure:
Transmitting controlled documents via standard email without encryption
Using shared cloud storage platforms with no access controls or audit trails
Accepting a generic ISO 27001 certificate without verifying scope
Failing to restrict subcontracting in the supplier agreement
Not logging the transfer in your internal export compliance system
For a deeper look at translation data security practices, the controls that satisfy NCA auditors are well-documented and implementable. The gap is almost always in execution, not awareness.
Need expert help with secure defense translation?
For compliance teams that need more than guidance, working with an LSP that is built for regulated environments makes a measurable difference. AD VERBUM’s AI+HUMAN hybrid translation workflow starts with ingesting your Translation Memories and Term Bases, runs controlled generation through a proprietary LLM-based LangOps System hosted on EU servers, and then routes every output through certified subject-matter expert review aligned to ISO 17100 and ISO 18587. The entire process is governed by ISO 27001 certified infrastructure with no reliance on public cloud tooling.
AD VERBUM holds ISO 27001 and ISO 17100 certifications and is actively pursuing AQAP 2110 alignment, which is the NATO quality assurance standard for defense suppliers. That combination gives EU defense primes a documented compliance baseline to present to Bafa, DGA, UAMA, or any other NCA during an audit. If your current translation workflow cannot produce that documentation, it is worth reviewing your localization services options and exploring AD VERBUM’s regulated industry expertise before your next controlled project goes out the door.
Frequently asked questions
What counts as an ‘unlicensed transfer’ under EU Regulation 2021/821?
Making controlled defense technical data available to an unvetted party, including a translator, without proper authorisation is an unlicensed transfer. The regulation covers technology in all formats, not just physical goods crossing a border.
Are intra-EU translations exempt from export controls?
No. Sensitive Annex IV items and items on national military control lists may require authorisation even for intra-EU transfers. Member states including Germany and France maintain national lists that extend beyond the EU common list.
What steps should I take to vet a translation vendor for defense technical data?
Conduct corporate and linguist-level nationality checks, require end-user undertakings rather than standard NDAs, confirm EU-hosted private infrastructure, restrict subcontracting, and retain access logs for the NCA audit window.
Do translation workflows count as ‘technical assistance’ under EU law?
Yes. Article 2(9) defines technical assistance as any transmission of working knowledge or technology by any means, which includes making a controlled document available to a linguist for translation purposes.
Recommended